What is business Intelligence? It is simply a system that gives a view of the company's past and current activities. It can manage financial, operational and sales data. Business intelligence applications can also deal with other sources of information such as customer and competitor benchmarking information. You can read more about business intelligence in our article. Also, read on to learn more about the various types of business intelligence. Listed below are some of the most common types of business intelligence.
Data visualization
Data visualization software allows companies to convert raw numbers into readable data. Users can see patterns and trends in the data, which allows them to identify opportunities for increased revenue. Our brains are wired to process visuals faster than text. On average, we can process 13 milliseconds. As a result, people often prefer to view these information in a visual format instead of reading it. Here are some benefits of data visualization in business Intelligence.
A user-friendly presentation requires effective interaction between data visualizations. The visualization should allow users to filter data, link different data visualizations, and drill down to a more comprehensive analysis. 3D visualizations are fine, but not for everyday business use. Additionally, data visualizations should not be cluttered with too much information, or have an unsuitable scale. Data visualization should be easy but informative for maximum effectiveness.
Processing in-memory databanks
The speed of in-memory data processing for business intelligence applications (BI) is a significant advantage. In-memory storage allows business intelligence applications to run at a much faster speed than traditional disk storage. In-memory BI apps can also perform complex calculations much faster than ever before. You'll be able view and update your business information in realtime with in-memory process.
BI tools store historical data in memory databases systems. The system is read-only because the data is stored in RAM. This feature is useful to users as it allows them to execute queries quicker on frequently updated information. In-memory analysis also reduces the need to index data pre-aggregated. It also reduces IT cost. A business can perform queries much quicker because the data is always up-to-date in real time.
Traditional databases have many benefits. However, large-scale businesses will find in-memory technology useful. This database can handle data up to 1.5PB. This database acts as a system-of-record, which eliminates the need to store data. In-memory storage allows for high-resolution data access. This allows multiple concurrent users to access data at high speeds.
Ad hoc Analysis
Ad hoc business intelligence analysis is vital. Financial departments are stuffed with financial facts and KPIs. But what happens when a business needs to drill into its data to uncover trends or understand why a certain number is higher than another? Ad hoc analysis can be a valuable tool. It allows businesses to make better decisions and makes the company transparent.
Data exploration was traditionally a skill reserved for the best data analysts. With the advent adhoc analysis, anyone can examine data without needing to know SQL. This type is great for micro-level decision making, such as the "What drove the highest number of marketing qualified leads last week?"
Self-service tools
Self-service tools for business intelligence (BI) can solve bandwidth issues and allow teams to run reports on their own. While self-service tool's speed and ease are appealing, they can cause more changes than your organization is ready for. Many BI tools can make it easier to create reports or model data. However, they could also lead to reports not being relevant to you business or not meeting your standards. You may need to use additional security procedures in these situations.
Traditional BI tools require data analysts to have access to IT personnel to create custom scripts and write SQL queries. Self-service BI tools are available that allow end users to create, deploy and manage reports and analyses by themselves without the need of IT specialists. The tools are easy to use, are inexpensive, and do not require highly technical expertise. The tool can be accessed and used via a browser. This allows users to gain insight and data. Using them can make it easier for analysts to understand the company's operations and identify opportunities for improvement.
FAQ
What Are the Benefits of Learning Information Technology on Your Own?
Without paying for classes, you can learn information tech on your own. You'll have access to all necessary resources, including books, software, and online courses. You won't have to worry about finding time to attend class, traveling to school, and dealing with other students. Plus, you will save money.
You may also be interested in becoming certified. The benefits of certification are numerous, but they include professional development opportunities, job placement assistance, and business networking.
There are many options for becoming certified in information technology. One option is to enroll in a self paced training program through Pearson VUE. There are hundreds of certification exams available, including CompTIA Security+ Certification, CompTIA Security+ Certification, CompTIA CompTIA Office Specialist, CompTIA Security+ Certification, CompTIA Security+ Certification, CompTIA Security+ Certification, CompTIA Security+ Certification, CompTIA Security+ Certification, and VMware Certified Professional Data Center Virtualization.
What are the steps to get cyber security certification?
For anyone who works in the IT sector, cyber security certifications are highly valued. CompTIA Security+ (1) Microsoft Certified Solutions Associate – Security(2) and Cisco CCNA Security Certification(3) are the most well-known courses. These courses are well-recognized by employers and provide a strong foundation upon which to build. However, there are many other options such as Oracle Certified Professional – Java SE 7 Programmer (4) and IBM Information Systems Security Foundation (5).
The choice is yours, but make sure you know what you're doing!
What are the future trends in cybersecurity?
The security industry is constantly evolving at an unimaginable rate. New technologies are emerging, old ones are getting updated, and existing ones are becoming obsolete. At the same time, the threats we face are constantly changing as well. Our experts will provide you with an overview of current events and deep dives into recent developments.
Everything you need is here
-
Check out the most recent news regarding new vulnerabilities or attacks
-
Use best practice strategies to combat the latest threats
-
This guide will help you stay ahead of the curve
You have many things to look forward towards in the near future. But the reality is that there is no way to predict what lies beyond. Therefore, we can only plan for these next few years and pray that luck comes our way.
However, if you really want to know what the future holds, then all you need to do is read the headlines. They tell us that the greatest threat isn't currently coming from hackers or viruses. Instead, it's governments.
Everywhere you look, governments all over the world try to spy on citizens. They use advanced technology, such as AI, to monitor people's online activities and track their movements. To build detailed profiles of individuals or groups, they collect data from everyone they meet. They don't believe privacy is important because they view it as a threat to national security.
This power has been used by governments to target individuals. In fact, some experts believe that the National Security Agency has already used its powers to influence elections in France and Germany. While it's not known if the NSA intended to target these countries in any way, it seems logical when you think about this. If you want to control your population, then you must ensure they are not in your way.
This isn't just a hypothetical scenario. History has shown that dictatorships often hack into opponents' phones and steal their data. There seems to be no limit to the extent that governments can do to maintain control over their subjects.
Although you may not be concerned about government surveillance, corporate spying might still concern you. There isn't any evidence that big business may be monitoring what you do online. Facebook, for instance, can track your browsing history no matter if you have granted permission. Google claims it doesn’t sell your data, but there isn’t any proof.
In addition to being concerned about what happens when governments are involved, you also need to consider how to protect yourself when it comes to corporations. It is a good idea to learn about cybersecurity if you are going to work in IT. You could prevent companies accessing sensitive information. You could also teach employees how to spot potential phishing schemes and other forms of social engineering.
Cybercrime is, in short, one of the most pressing problems facing our society today. Hackers, governments, criminals, and terrorists all work together to steal your personal information and destroy your computer systems. There are solutions. You just need to know where to look.
How do I prepare for my certification exams?
There are many options for how to prepare. The first is to read the syllabus carefully before taking the exam. Another option is to read the entire content of the exam guidebook before sitting the exam. To test your knowledge of the topics, you can try a few questions. The last option is to enroll in a local community college so you can interact directly with students who have completed the same certification exam.
Numerous websites offer free exam prep materials. However, you can only purchase one electronic copy of the exam manual. This copy should be saved safely. A CD/DVD drive is a good choice.
Keep in mind that some companies offer their own self-study guides. These usually cost between $100 and $400. They often come with additional features, such as flashcards or quizzes. Some of these products even allow you to take the exam online.
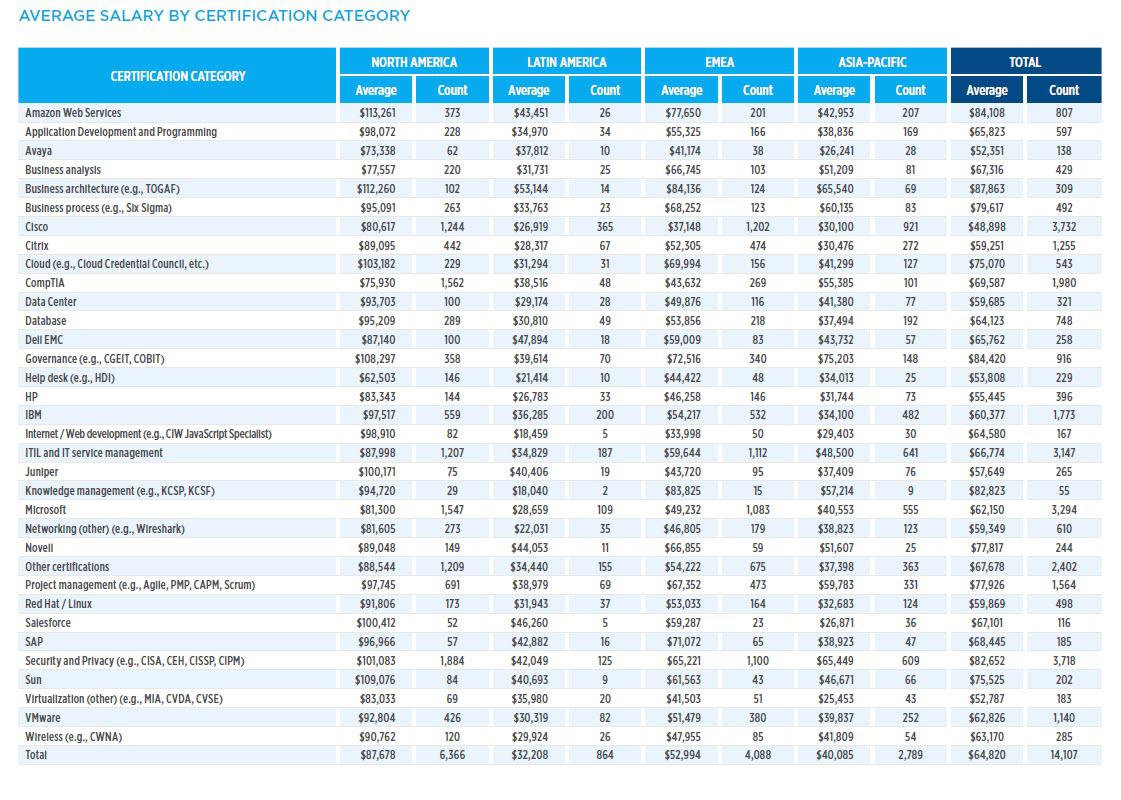
What is the monthly salary for an IT job?
The average annual salary for Information Technology professionals in the UK stands at PS23,000. This includes salary and bonus. A typical IT Professional would earn approximately PS2,500 per calendar month.
Some IT professionals have the opportunity to earn more than PS30,000 annually.
It is generally accepted that you need to have at least 5-6 years experience before you can make a decent salary in your chosen career.
Statistics
- The United States has the largest share of the global IT industry, accounting for 42.3% in 2020, followed by Europe (27.9%), Asia Pacific excluding Japan (APJ; 21.6%), Latin America (1.7%), and Middle East & Africa (MEA; 1.0%) (comptia.co).
- The top five countries contributing to the growth of the global IT industry are China, India, Japan, South Korea, and Germany (comptia.com).
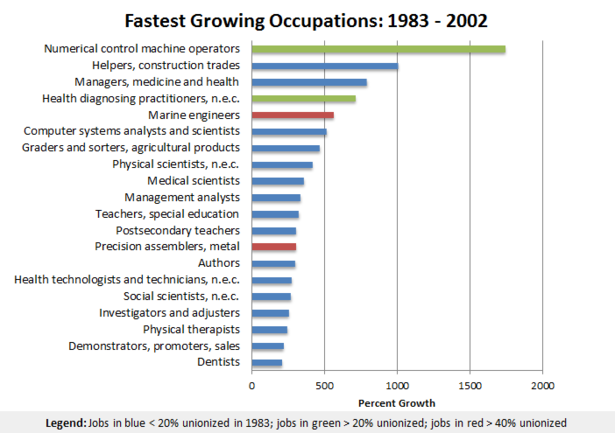
- Employment in computer and information technology occupations is projected to grow 11% from 2019 to 2029, much faster than the average for all occupations. These occupations are projected to add about 531,200 new jobs, with companies looking to fill their ranks with specialists in cloud computing, collating and management of business information, and cybersecurity (bls.gov).
- The global information technology industry was valued at $4.8 trillion in 2020 and is expected to reach $5.2 trillion in 2021 (comptia.org).
- The top five countries providing the most IT professionals are the United States, India, Canada, Saudi Arabia, and the UK (itnews.co.uk).
- The median annual salary of computer and information technology jobs in the US is $88,240, well above the national average of $39,810 (bls.gov).
External Links
How To
How do I start learning cyber security?
Many people are familiar with hacking if they have been working in computer technology for years. This may be confusing for some.
Hacking refers primarily to the use of viruses, trojans or spyware to gain unauthorised access computers, networks and other systems.
Cybersecurity has evolved into an industry, offering ways to protect yourself from these types of attacks.
It is important to understand how hackers work to help you stay safe online. Here are some tips to help you start your journey towards understanding cybercrime.
What is Cyber Security?
Cyber security refers to protecting computers against external threats. If hackers attempt to hack into your computer, they could have access to all your files and data.
There are two types, Computer Forensics vs Computer Incident Response Teams.
Computer forensics is the study of a computer's behavior after a cyberattack. It is performed by experts who look for evidence that could lead them to the culprit. Computers are checked for signs that indicate tampering, or damage due to malware or viruses.
The second type is CIRT. CIRT teams work together to respond to incidents involving computers. They use their expertise to stop attackers before they do significant harm.